Aim of Tutorial : To sniff passwords from all the users in LAN by ARP Poisioning in Linux Backtrack5.
Notice how there are no Hash (#) signs in front of the last two lines.
2.> Run Ettercap:
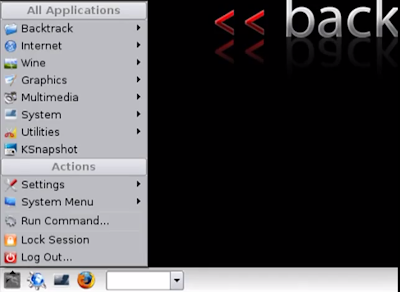
Now we can start Ettercap-GTK (This is a pretty version of the shell program, it gives us a nice GUI to play with). Ettercap-GTK can be found under: Menu -> Backtrack -> Privilege Escalation -> Spoofing -> Ettercap-GTK
3.> Setting up Sniffing:
Sniff -> Unified Sniffing
Eth0 -> OK ………………………..(This runs Sniffing on your first Ethernet card)
Hosts -> Scan for hosts ………… (Scans the network for targets)
Hosts -> Hosts List ………………….(Opens your hosts list
4.> Targeting the Hosts on the gateway:-
Now, you have all the computers on the network on the host list. If you want to only scan one computer (its better and quicker for us to just do the one) then click on the default gateway first, and click the target 1 button.
After you do the default gateway, then click your computer you are attacking and make it “Target 2” by selecting it and clicking the “target 2” button.
5.> After setting up the sniffing:
Mitm -> ARP poisoning -> Select “Sniff remote connections” Hit OK
Start -> Start Sniffing
Your done! Now you are sniffing the computer for passwords onto certain websites that use SSL for their security. When you are done go to: Start -> Stop Sniffing, and then go to Mitm -> Stop mitm attack(s)
Note: If in case you wish to check whether the ARP poisoning was successful or not you can select Plugins from the menu bar and select, Check Poisson plugin, It takes a little while to show the message " Poisoning was successful :)"
Read more...
Ettercap:
Ettercap is a tool for network protocol analysis and security auditing. It has the ability to intercept traffic on a network, capture passwords, and conduct active eavesdropping against common protocols.
For this exercise I will be using ARP Poisoning to sniff the LAN for passwords that use SSL (Hotmail, Gmail, Etc.)
ARP:
“Address Resolution Protocol”: As defined by Wikipedia: ARP is a computer networking protocol for determining a network host's link layer or hardware address when only its Internet Layer (IP) or Network Layer address is known. This function is critical in local area networking as well as for routing internetworking traffic across gateways (routers) based on IP addresses when the next-hop router must be determined.
So in normal terms ARP is the way that we get a MAC address of a Host or Node from the IP address.
ARP Spoofing:
This is the technique we will use to attack a wired or a wireless network. ARP Spoofing allows the attacker to sniff data frames from the LAN, then gives you the ability to modify the traffic (good for redirecting to your own computer to download an exploit to victim), or stop the traffic from entering the network, or a specific computer (good for local DOS Attacks on a Local Area Network).
The idea behind the attack is to send a fake (AKA “Spoofed”) ARP message to the LAN. Any traffic on the network meant for that IP address that you attacked (whole network if you want) will be sent to the attacker. The attacker (you) can choose to forward the traffic to the actual gateway (Passive Sniffing) or modify the data before forwarding it (Man in the Middle).
How we will do it for this exercise:
1.> Edit a file:
We first have to edit one file (Don’t worry, we just have to delete two # signs to “uncomment” them).
The file we will be editing is called etter.conf and it can be found under the etc folder. (Full Path = /etc/etter.conf) with this command in terminal :-
Ettercap is a tool for network protocol analysis and security auditing. It has the ability to intercept traffic on a network, capture passwords, and conduct active eavesdropping against common protocols.
For this exercise I will be using ARP Poisoning to sniff the LAN for passwords that use SSL (Hotmail, Gmail, Etc.)
ARP:
“Address Resolution Protocol”: As defined by Wikipedia: ARP is a computer networking protocol for determining a network host's link layer or hardware address when only its Internet Layer (IP) or Network Layer address is known. This function is critical in local area networking as well as for routing internetworking traffic across gateways (routers) based on IP addresses when the next-hop router must be determined.
So in normal terms ARP is the way that we get a MAC address of a Host or Node from the IP address.
ARP Spoofing:
This is the technique we will use to attack a wired or a wireless network. ARP Spoofing allows the attacker to sniff data frames from the LAN, then gives you the ability to modify the traffic (good for redirecting to your own computer to download an exploit to victim), or stop the traffic from entering the network, or a specific computer (good for local DOS Attacks on a Local Area Network).
The idea behind the attack is to send a fake (AKA “Spoofed”) ARP message to the LAN. Any traffic on the network meant for that IP address that you attacked (whole network if you want) will be sent to the attacker. The attacker (you) can choose to forward the traffic to the actual gateway (Passive Sniffing) or modify the data before forwarding it (Man in the Middle).
How we will do it for this exercise:
1.> Edit a file:
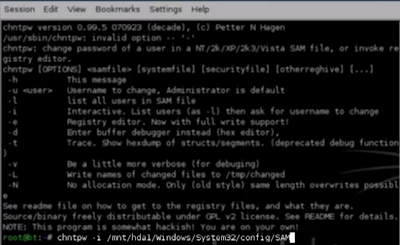
We first have to edit one file (Don’t worry, we just have to delete two # signs to “uncomment” them).
The file we will be editing is called etter.conf and it can be found under the etc folder. (Full Path = /etc/etter.conf) with this command in terminal :-
gedit /etc/etter.conf
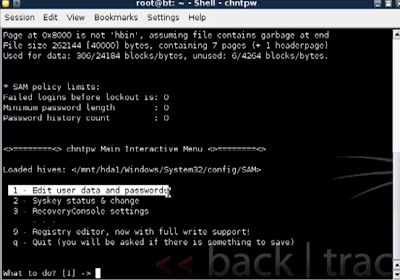
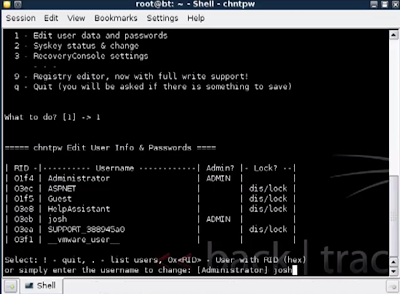
We need to change the part under the “redir_command_on/off” section.
MAKE SURE YOU ONLY UNCOMMENT THE TWO LINES UNDER “if you use iptables”
The Linux subsection will look like this when done:
We need to change the part under the “redir_command_on/off” section.
MAKE SURE YOU ONLY UNCOMMENT THE TWO LINES UNDER “if you use iptables”
The Linux subsection will look like this when done:
Code:
#---------------
# Linux
#---------------
# if you use ipchains:
#redir_command_on = "ipchains -A input -i %iface -p tcp -s 0/0 -d 0/0 %port -j REDIRECT %rport"
#redir_command_off = "ipchains -D input -i %iface -p tcp -s 0/0 -d 0/0 %port -j REDIRECT %rport"
# if you use iptables:
redir_command_on = "iptables -t nat -A PREROUTING -i %iface -p tcp --dport %port -j REDIRECT --to-port %rport"
redir_command_off = "iptables -t nat -D PREROUTING -i %iface -p tcp --dport %port -j REDIRECT --to-port %rport"
Notice how there are no Hash (#) signs in front of the last two lines.
2.> Run Ettercap:
Now we can start Ettercap-GTK (This is a pretty version of the shell program, it gives us a nice GUI to play with). Ettercap-GTK can be found under: Menu -> Backtrack -> Privilege Escalation -> Spoofing -> Ettercap-GTK
3.> Setting up Sniffing:
Sniff -> Unified Sniffing
Eth0 -> OK ………………………..(This runs Sniffing on your first Ethernet card)
Hosts -> Scan for hosts ………… (Scans the network for targets)
Hosts -> Hosts List ………………….(Opens your hosts list
4.> Targeting the Hosts on the gateway:-
Now, you have all the computers on the network on the host list. If you want to only scan one computer (its better and quicker for us to just do the one) then click on the default gateway first, and click the target 1 button.
After you do the default gateway, then click your computer you are attacking and make it “Target 2” by selecting it and clicking the “target 2” button.
5.> After setting up the sniffing:
Mitm -> ARP poisoning -> Select “Sniff remote connections” Hit OK
Start -> Start Sniffing
Your done! Now you are sniffing the computer for passwords onto certain websites that use SSL for their security. When you are done go to: Start -> Stop Sniffing, and then go to Mitm -> Stop mitm attack(s)
Note: If in case you wish to check whether the ARP poisoning was successful or not you can select Plugins from the menu bar and select, Check Poisson plugin, It takes a little while to show the message " Poisoning was successful :)"